Blockaid recently pinpointed and red-flagged that the Aftermath Finance’ perpetuals trading system on the Sui Network was under active exploitation.
The alert spread like wildfire within the crypto community, sounding alarms that a vulnerability had allowed an attacker to steal significant amounts of funds in mere minutes.
The analysis shows that $1.1 million in USDC were pulled from the protocol in 11 fast transactions over 36 minutes. The attacker leveraged a vulnerability in the fee accounting mechanism of the clearing house linked to an address.
In the world of decentralized finance (DeFi), if an exploit is capable enough to take over critical financial operations such as fee calculation and collateral management, it’s a matter of seconds or minutes that attackers can capitalize on it.
Fees Become Earnings With Integer Overflow Bug
At the heart of the exploit lay a base-level integer overflow bug, a programming surprisingly common for complex decentralized systems with many inter-components.
Fee values were stored as unsigned 256-bit integers (u256) that can not represent negative numbers at all. What happened was that in one part of the system, these values were misinterpreted as signed integers (which can hold both positive and negative values).
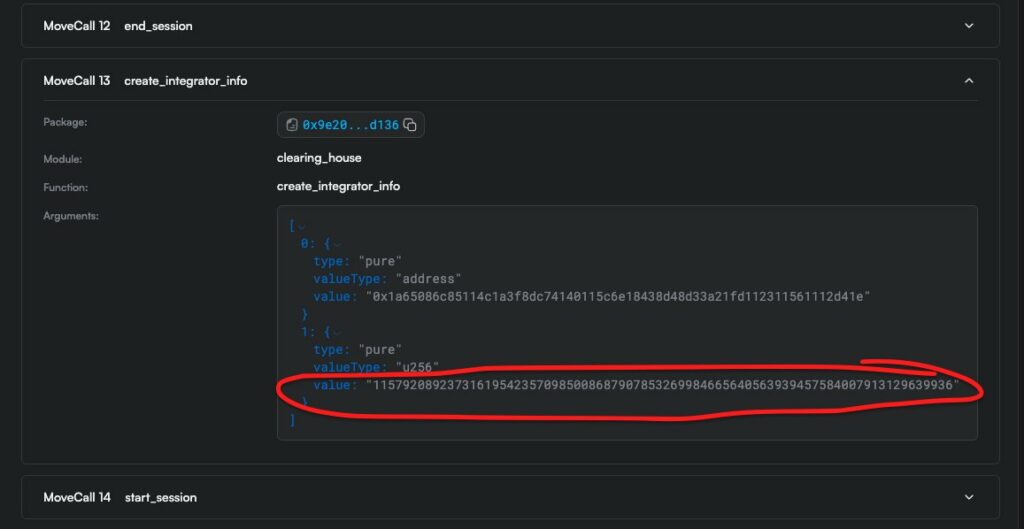
They used that to get a wrap around by submitting a number just below the top of a u256. As a signed integer, it was read to a large negative number. This inversion of the fee structure turned fees that ought to have been charged into payouts. As a result, the protocol started paying for trade executions to the attacker who was then able to create synthetic collateral and immediately withdraw directly from the protocol’s vault.
On-Chain Data Confirms Absence of Validation Safeguards
The mechanics of the exploit are well established on the blockchain transaction records. It recorded payouts for those effectively negative fees and then rewarded the attacker, instead of receiving fees in return.
The system took inputs in a way that did not apply any arbitrary restriction on those input values, and accepted malicious parameters which contradicted its assumption about the object.
The lack of strong input validation is one of the fundamental design errors. In such cases, validating input parameters to be in the expected ranges provides a secure system architecture against such exploitations.
Expanding Scope Of Parameters Validation Issues
The Aftermath exploit is one of several such parameter validation lapses by multiple DeFi protocols that have been observed in April.
Recent instances include:
Singularity, where an oracle fee tier of 42 was invalid based on the supported tiers of 100, 500, 3000 and 10000.
The root cause in all cases being setter functions that were not enforcing constraints on what input values could have been, separate from assumptions made elsewhere in the system.
Security researchers have observed that attackers are now increasingly using AI-powered tools to automatically probe edge cases and uncover boundary conditions missed by human developers, while defenders are starting to integrate similar automated tools into their security audits.
Even though the exploit was severe, the response of the ecosystem was immediate and effective. Aftermath Finance immediately moved to halt the breach and protect users, assisted by Mysten Labs and the Sui Foundation.
It said that the protocol would cover the total losses by compensating all impacted users fully. This method is an embodiment of the commitment held by more DeFi projects to protect users and maintain credibility in times of insecurity.
The Aftermath team said in an official statement that it believes this should be business as normal soon and praised the quick response of Blockaid and partnering organizations.
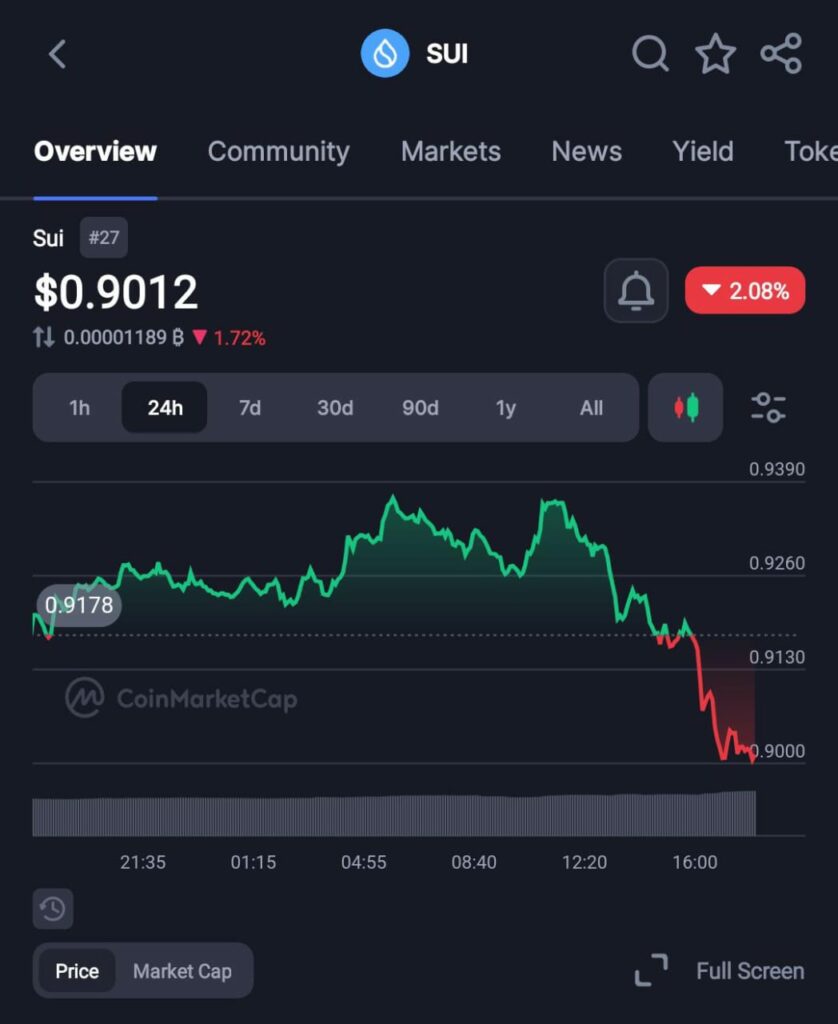
Sui Price Holds Stable But Confidence Shaky
Importantly, the exploit did little to affect the wider market of the Sui tokens. The token price fell slightly (about – 2%) to $0.90 at the time of writing. Such relative stability indicates that market actors appear to consider the incident a case of material protocol-level failings, rather than a systemic and critical flaw in the Sui Network itself.
It also emphasizes the important difference between application-level vulnerabilities and blockchain infrastructure ones. Aftermath clarified the exploit was not due to the Move programming language that powers Sui, but rather bugs in the implementation of the protocol.
The incident with Aftermath Finance is an unfortunate reminder that air-gapped solutions for protecting Decentralized Finance systems are far from solved. Even seemingly benign vulnerabilities (like integer overflows) in complex smart contract environments can inflict serious damage when not looked for and managed.
With the growth of DeFi over time, the need for extensive testing, auditing and monitoring in real-time becomes clear. Design protocols not only for expected use, but to anticipate adversarial behaviors that test systems to their extreme boundaries.
AI as a tool for offense and defense marks the beginning of robustness in blockchain as an ecosystem. As attackers scale up their operations through automation to hunt for weaknesses, developers are reaching for similar technologies to optimize audits.
User funds have been secured and recovery is underway at Aftermath Finance, with the immediate crisis seemingly now contained. But we can be sure that the lessons from this situation will shape how security and resilience are approached across the industry in a changing and complex landscape.
Disclosure: This is not trading or investment advice. Always do your research before buying any cryptocurrency or investing in any services.
Follow us on Twitter @themerklehash to stay updated with the latest Crypto, NFT, AI, Cybersecurity, and Metaverse news!